Monitor and correlate data for the Cisco Cloud Security Umbrella Splunk Add-On
Cisco Cloud Security Umbrella Add-On For Splunk
The Cisco Cloud Security Umbrella Add-On integrates your Umbrella event data with Splunk. The add-on reads data into the Splunk platform from your configured data sources.
This guide describes how to install the Cisco Cloud Security Umbrella Add-On for Splunk on your instance of Splunk (on-premises or cloud) and configure data inputs for Umbrella.
About the Cloud Security Umbrella Add-On
In the Cisco Cloud Security Umbrella Add-On, you configure data inputs for the types of events in your Umbrella organization. Then, Splunk indexes the data for the event types and displays the events on the Umbrella dashboards in Splunk.
In the add-on, set up these data inputs:
- DNS logs
- Proxy logs for the Secure Web Gateway (SWG)
- Firewall logs
- Audit logs
- Data Loss Prevention (DLP) logs
The Cisco Cloud Security Umbrella Add-On for Splunk is available at,
https://classic.splunkbase.splunk.com/app/5557/
What's New
Updates to the Cisco Cloud Security Umbrella Add-On for Splunk.
Cisco Cloud Security Umbrella Add-On Version 1.0.33
- Added support for the v7 and v8 proxy (Umbrella Secure Web Gateway) log formats.
- Added support for the Umbrella Data Loss Prevention (DLP) log input.
- Fixed issues that are related to timezones.
Prerequisites
- Splunk Enterprise, Splunk Cloud
- Splunk platform versions: 9.2, 9.1, 9.0
- Access to Cisco Umbrella
- Access to your own or Cisco managed AWS S3 bucket
- Splunk administrative privileges
Previous Releases
Information about previous Cisco Cloud Security Umbrella Add-On for Splunk software releases.
Cisco Cloud Security Umbrella Add-On Version 1.0.28
- Updated Umbrella Secure Web Gateway (SWG) and Cloud Delivered Firewall (CDFW) logs to the v6 Umbrella log format.
- Rebuilt with add-on builder 4.x.
- Added Umbrella Admin Audit log as an event type. Store the Umbrella Admin Audit logs in the Splunk indexer.
- Fixed security vulnerabilities and upgraded library.
Prerequisites
- Splunk version 8.2.0 and later
- Access to Cisco Umbrella
- Access to your own or Cisco managed AWS S3 bucket
- Splunk administrative privileges
Install Cloud Security Umbrella Add-On
- Navigate to Splunkbase at
https://splunkbase.splunk.com/.
- Search for Cisco Cloud Security.
- Download and install the Cisco Cloud Security Umbrella Add-On.
- Restart your Splunk instance to complete the installation of the add-on.
Install Cloud Security Umbrella Add-On in Distributed Deployments
You can install the Cloud Security Umbrella Add-On in a distributed deployment of Splunk Enterprise, or any deployment where you use forwarders to retrieve your data. Depending on your environment and preferences, and the requirements of the add-on, you can install the add-on in multiple environments.
We recommend that you only install the Cisco Cloud Security Umbrella Add-On using the Splunk heavy forwarder and Splunk indexes.
| Splunk Platform Component |
Support |
| Heavy Forwarder |
Best Practice. |
| Indexer |
Supported if no heavy forwarders are enabled. |
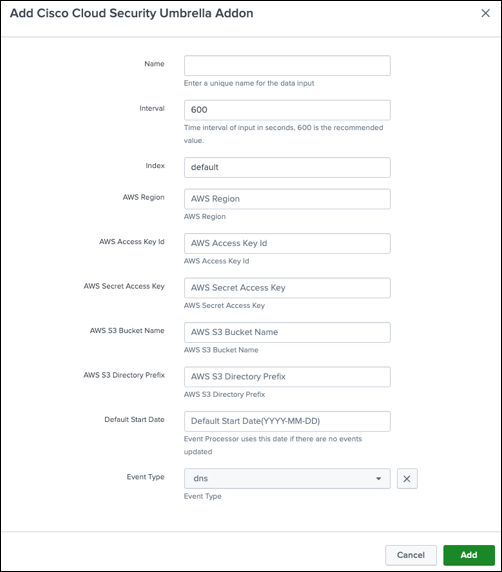
Add an input and set up the integration of event data from your own or Cisco-managed S3 bucket with Splunk. Each line in a log file is processed and written to Splunk as a single event.
Note: We recommend that you provide a unique name for each input.
Navigate to Application Settings.
Accept the terms and conditions, and then click Submit.

Navigate to Inputs, and then click Create New Input.

Enter a Name, Interval, Index, your AWS S3 bucket settings, Default Start Date, and Event Type.
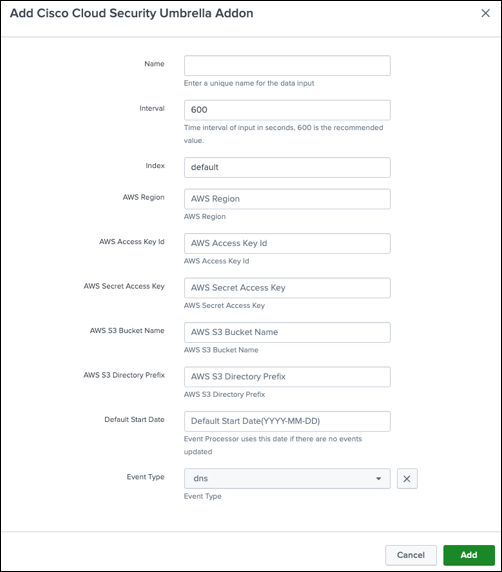
Name—Enter a name for the data input.
Interval—Provide an interval (in seconds) to fetch the data to the Splunk indexer. We recommend 600 seconds.
Index—Choose the index where to store the Umbrella logs. We recommend that you do not choose the default index.
AWS Region—Enter your AWS S3 region, for example: us-west-1.
AWS Access Key Id—Enter your AWS Access Key ID.
AWS Secret Access Key—Enter your AWS Secret Access Key.
AWS S3 Bucket Name—Enter your AWS S3 Bucket Name, for example: cisco-managed-us-west-1.
AWS S3 Directory Prefix—Enter the AWS S3 Directory Prefix and append it with a forward slash (/).
Sample logs from a Cisco-managed Bucket
| Event Type |
Example |
| dns |
2506xxx_2db1xxxx1ddf7cxxx18652xxxxfdab7xxxxd60xx/dnslogs/ |
| proxy |
2506xxx_2db1xxxx1ddf7cxxx18652xxxxfdab7xxxxd60xx/proxylogs/ |
| firewall |
2506xxx_2db1xxxx1ddf7cxxx18652xxxxfdab7xxxxd60xx/firewalllogs/ |
| audit |
2506xxx_2db1xxxx1ddf7cxxx18652xxxxfdab7xxxxd60xx/auditlogs/ |
| dlp |
2506xxx_2db1xxxx1ddf7cxxx18652xxxxfdab7xxxxd60xx/dlplogs/ |
Default Start Date—Enter a date in the YYYY-MM-DD format, for example: 2022-02-27. We recommend that you set the Default Start Date to the date when you installed the app. Selecting a date before the date when you installed the app may create a backlog of events that the app must process.
Event Type—Choose the event type, for example: dns, firewall, proxy, audit, or dlp.
Repeat steps 1–4 to configure more data inputs.
Note: If you upgrade the Cisco Cloud Security Umbrella app, you must reenter the AWS Secret Access Key. We recommend that you do not edit the Default Start Date when you reenter the AWS Secret Access Key.
View Umbrella Events in Cloud Security Umbrella App
View your configured events in the Umbrella dashboard from the Cloud Security Umbrella App. For more information, see View Umbrella Dashboard.
Support
If you have questions about the Cisco Cloud Security Umbrella Add-On, contact Cisco Umbrella Support.