├
|
![[V]](styles/eye.gif) |
pol:Obj Represents a generic policy object. |
|
├
|
![[V]](styles/eye.gif) |
pol:Def Represents self-contained policy document. |
|
|
├
|
![[V]](styles/eye.gif) |
aaa:AuthRealm An authentication realm provides authentication to verify the identity of an entity (person or device) accessing fabric devices. The authentication is based on the user ID and password combination provided by the entity trying to access the fabric. Authentication can be performed locally, using the local lookup database, or by remote, using one or more RADIUS or TACACS+ servers. |
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Definition The AAA policy definition. This is an abstract class and cannot be instantiated. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:ADomainRef This object is generated and used only by internal processes. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:DomainRef A reference to the domain that the parent object belongs to. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:IDomainRef This object is generated and used only by internal processes. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:AProvider An abstract class that is the superclass for the Radius/Tacacs/Ldap provider classes. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:LdapProvider An LDAP provider is a remote server supporting the LDAP protocol that will be used for authentication. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:RadiusProvider A RADIUS provider is a remote server supporting the RADIUS protocol that will be used for authentication. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:TacacsPlusProvider A TACACS+ provider is a remote server supporting the TACACS+ protocol that will be used for authentication. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:ARbacRule This is generated and used only by internal processes. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:IPRbacRule IPRbacRule mos are created under aaaRbacEp as a side-effect of the creation of PRbacRule under fv:Tenant |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:IRbacRule This is generated and used only by internal processes. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:RbacRule A role based access control (RBAC) rule allows users from a security domain to read the subtree starting at a specific object. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Banner An abstract class that contains login banners and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:PreLoginBanner A GUI banner is the informational banner to be displayed before user login authentication. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Config The generic security authentication configuration. This is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:AuthMethod The generic security authentication method.
This is an abstract class and cannot be instantiated. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:DefaultAuth The default authentication configuration for all login methods. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Domain An AAA domain is the AAA security method for processing authentication requests. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Ep The base class for an AAA endpoint is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:LdapEp The global security management properties for LDAP endpoints
and LDAP provider groups. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:RadiusEp The RADIUS endpoint policy is the global security management properties for RADIUS endpoints
and RADIUS provider groups. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:TacacsPlusEp The TACACS+ endpoint policy is the global security management properties for TACACS+ endpoints
and TACACS+ provider groups. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:LdapGroupMapRule
The MO represents an LDAP Group Map Rule
The actual Map consisting of Domains and Roles
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:LoginDomain An AAA login domain for authentication and authorization. The AAA configuration can be configured per domain. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:ProviderGroup A provider group is a set of providers that will be used by the system during the authentication process. During authentication, all the providers within a
provider group are tried in order. If all of the configured servers are unavailable or unreachable, the system manager automatically falls back to the local
authentication method using the local username and password. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:LdapProviderGroup An LDAP provider group is a group of remote servers supporting the LDAP protocol for authentication. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:RadiusProviderGroup A RADIUS provider group is a group of remote
servers supporting the RADIUS protocol for authentication. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:TacacsPlusProviderGroup A TACACS+ provider group is a group of remote servers supporting the TACACS+ protocol for authentication. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:PwdProfile The password profile contains the information about password constraints that apply to all local users. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:RbacEp This is generated and used only by internal processes. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Realm The AAA realm is the security method for processing authentication and authorization requests. The realm allows the protected resources on the associated server to be partitioned into a set of protection spaces, each with its own authentication authorization database. This is an abstract class and cannot be instantiated. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:Role An AAA role is a set of attributes and privileges that describe what a user is authorized to perform. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:SshAuth A user's public key in PEM format used for certificate-based login. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:SystemUser The base class for a system user.
This is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:User A locally-authenticated user account. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:UserCert An AAA user certificate in X.509 format. This certificate is the
RSA public key used for certificate-based REST API calls. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:UserData This object is managed internally and should not be modified by the user. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:UserEp A user endpoint is a local user. A user is assigned a role determines the user's privileges, and belongs to a security domain, which determines the user's scope of control |
|
|
├
|
![[V]](styles/eye.gif) |
cap:Def A base class for capabilities. |
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptcap:AMfgDef The manufacturing-related properties such as PID and SKU. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptcap:MfgDef The manufacturing-related properties such as PID and SKU. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptcap:SfpMfgDef The small form-factor pluggable transceiver (SFP) manufacturing-related properties. |
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:DomP SHIV TODO: Need to find a propert Super class SHASHANK TODO: Need to add other roles/access besides admin |
|
|
├
|
![[V]](styles/eye.gif) |
cloud:AL3TunnelIfP IPSec tunnel running on the NIC. The outer tunnel desination address is
on-prem IPN router's public address. The tunnel source address is parent
interface's primary address. |
|
|
├
|
![[V]](styles/eye.gif) |
cloud:AVpnGwPol Shiv TODO uncomment for next release mo name="DirectConnPol"
concrete="yes"
super="pol:Def"
access="admin"
label="Cloud Direct Connect Policy"
>
... |
|
|
├
|
![[V]](styles/eye.gif) |
cloud:CtxHolder Mo that will be used to pull
cloudCtxProfileDef from PM to cPE |
|
|
├
|
![[V]](styles/eye.gif) |
cloud:DefCont Container for all the cloud:DefCont, under top, to
have them neatly organized |
|
|
├
|
![[V]](styles/eye.gif) |
comm:Pol The communication policy contains the service configuration for various services. |
|
|
├
|
![[V]](styles/eye.gif) |
comp:AccessP An abstract base class for policies related to access credentials. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vmm:UsrAccP The user account profile is used to access a VM provider account. |
|
|
├
|
![[V]](styles/eye.gif) |
condition:RetP The condition log record retention policy specifies the maximum number of log records to be retained and the maximum number of log records to be deleted in a 30-second period. |
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:ARetP The audit log retention policy specifies the maximum number of audit log records to be retained and the maximum number of audit log records to be deleted in a 30-second period. Note that this is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:CtrlrRetP The controller audit log retention policy specifies the maximum number of controller audit log records to be
retained and the maximum number of controller audit log records to
be deleted in a 30-second period. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
aaa:SwRetP The switch AAA audit log retention policy specifies the maximum number of AAA audit log records to be retained and the maximum number of AAA audit log records to be deleted in a 30-second period. |
|
|
|
├
|
![[V]](styles/eye.gif) |
event:ARetP The event record retention policy, which specifies the maximum number of event history records to be retained on the node or controller and the maximum number of event history records to be deleted in a 30-second period. Note that this is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
event:CtrlrRetP The controller event record retention policy, which
specifies the maximum number of controller event records to be
retained and the maximum number of controller event records to
be deleted in a 30-second period. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
event:SwRetP The switch event retention policy specifies the maximum number of event records to be retained and the maximum number of
event records to be deleted in a 30-second period. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fault:ARetP The fault record retention policy specifies the maximum number of fault history records to be retained on the node or controller and the maximum number of fault history records to be deleted in a 30-second period. Note that this is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fault:CtrlrRetP The controller fault record retention policy specifies the maximum number of controller fault records to be
retained and the maximum number of controller fault records to
be deleted in a 30-second period. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fault:SwRetP Specifies the maximum number of fault records to be retained and the maximum number of fault records to be deleted in a 30-second period. These settings can be changed either by creating a custom policy or editing the default policy. |
|
|
|
├
|
![[V]](styles/eye.gif) |
health:ARetP The health score history record retention policy, which specifies the maximum health score history record count to delete in a 30-second period. Note that this is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
health:CtrlrRetP The controller health score history record retention policy, which specifies the maximum number of controller health score history
records to be retained and the maximum number of controller health score history records to be deleted in a 30-second period. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
health:SwRetP The switch health retention policy specifies the maximum number of health score history records to be retained and the maximum
number of health score history records to be deleted in a 30-second period. |
|
|
├
|
![[V]](styles/eye.gif) |
copp:AProfile Abstract class for all the profiles for CoPP that can be applied at the node level |
|
|
├
|
![[V]](styles/eye.gif) |
datetime:APol The date time policy is based on international time zones and a defined NTP server. Before configuring a date and time policy under a domain group, this policy must first be created. Policies under the Domain Groups root were already created by the system and ready to configure. |
|
|
|
├
|
![[V]](styles/eye.gif) |
datetime:Pol The date time policy is based on international time zones and a defined NTP server. Before configuring a date and time policy under a domain group, this policy must first be created. Policies under the Domain Groups root were already created by the system and ready to configure. |
|
|
├
|
![[V]](styles/eye.gif) |
datetime:Format The date/time format policy defines the time-zone for the entire fabric. |
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:Filter The filter properties of the client-defined end point attached to the network. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpgToEp The endpoint group-to-endpoint atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpgToEpg The endpoint group-to-endpoint group atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpgToIp The endpoint group-to-IP atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:ToEpgCmn The abstract object with a destination endpoint group. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpToEpg The endpoint-to-endpoint group atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:IpToEpg The IP-to-endpoint group atomic counter policy detects drops and misrouting in the fabric and enables quick debugging and isolation of application connectivity issues. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpToAny The endpoint-to-any atomic counter policy which detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpToEp The endpoint-to-endpoint atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:EpToExt The endpoint-to-external IP address atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:IpToIp IP Addr to IP policy Defn. Used for an
external host identified by its IP address to
another IP address
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:TenantSpaceCmnDef The tenant space common definition. This atomic counter managed object is used internally for managing Epg/Epp source
and destination policies. |
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:ToEpCmn The abstract object for atomic counter with a destination endpoint. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:AnyToEp Atomic counters detect drops and misrouting in the fabric enables quick debugging and isolation of application connectivity issues. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgac:ExtToEp The external host-to-endpoint atomic counter policy detects drops and misrouting in the fabric to enable quick debugging and isolation of application connectivity issues. |
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:OptionPol The DHCP option policy, which defines lease duration, gateway routers, and other configuration parameters in what are called DHCP options. Every DHCP server must have one or more policies defined for it. The policies are especially useful if you have multiple scopes because you only need to define a policy once and apply it to the multiple scopes. You can define named policies with specific option definitions or you can use system defaults.
Note... |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsBtEcc The diagnostic test set for leaf fabric nodes to run at bootup on extended chassis cards (FEXes). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsBtLc The diagnostic test set for leaf fabric nodes to run at bootup on line cards (I/O cards). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsBtSc The diagnostic test set for leaf fabric nodes to run at bootup on supervisor cards. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:TsBtLeafP The diagnostic test set for leaf fabric ports to run at bootup on line cards (I/O cards). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsBtLc The diagnostic test set to run at bootup on spine line cards (I/O cards). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsBtScc The diagnostic test set to run at bootup on spine system controller cards. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsOdEcc The diagnostic test set for leaf fabric nodes to run on extended chassis cards (FEXes). |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsOdLc The diagnostic on-demand test set for leaf fabric nodes to run on line cards (I/O cards). |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsOdLc The diagnostic on-demand test set to run on spine line cards (I/O cards). |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsOdSc The diagnostic on-demand test set for leaf fabric nodes to run on supervisor cards. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsOdSc The diagnostic on-demand test set for leaf fabric nodes to run on spine supervisor cards. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SysCTsOd The on-demand abstract diagnostic policy for system controller cards. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsOdScc The diagnostic on-demand test set to run on spine system controller cards. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsHlEcc The diagnostic test set for leaf fabric nodes to run on extended chassis cards (FEXes). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsHlLc The diagnostic ongoing health test set for leaf fabric nodes to run on line cards (I/O cards). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:LeTsHlSc The ongoing diagnostic health test set for leaf fabric nodes to run on supervisor cards. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsHlFc The ongoing diagnostic health test set to run at bootup on spine fabric cards. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsHlLc The ongoing diagnostic health test set to run at bootup on spine line cards (I/O cards). |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsHlSc The ongoing diagnostic health test set to run at bootup on spine supervisor cards. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eqptdiagp:SpTsHlScc The ongoing diagnostic health test set to run at bootup on spine system controller cards. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:OSpineS Override Spine Selector
@@@ Its not configurable because theres no spine policy group in infra. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LeCardPGrp A leaf card policy group enables you to apply policies to a group of leaf cards. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpCardPGrp A spine card policy group enables you to apply policies to a group of spine cards. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LeNodePGrp A leaf node policy group enables you to apply policies to a group of leaf nodes. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpNodePGrp A spine node policy group enables you to apply policies to a group of spine nodes. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LePortPGrp The leaf port policy group enables you to apply policies to a group of leaf ports. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpAPortPGrp A base class for a spine port policy group. This is used for specifying policies to be applied to the spine ports consuming this policy group. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpPortPGrp A spine port policy group enables you to apply policies to a group of spine ports. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:CtrlrPGrp The controller policy group enables you to apply policies to a group of controllers. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:PodPGrp A POD policy group enables you to apply policies to the leaf nodes that are part of this POD. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccBndlGrp The bundle interface group enables you to specify the interface policy you want to use. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccPortGrp The interface policy group enables you to specify the interface policies you want to use. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccBndlSubgrp The access bundle subgroup enables you to specify (override) a different LACP member policy name for some of the interfaces that are part of an access bundle group. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccCardPGrp The module policy group enables you to specify the module policies you want to use. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccNodePGrp The node policy group enables you to specify the node policies you want to use. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:CardP The template used for deploying card fabric configuration. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LeCardP The leaf card profile is a template used for deploying the card fabric configuration on a leaf. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpCardP A spine card profile is used for deploying the card configuration on the spine. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:CtrlrP The controller profile. This object represents the template used for deploying controller-level configuration. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:NodeP The node profile. This is the template used for deploying node fabric configuration. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LeafP The leaf profile is a template used for deploying the leaf fabric configuration. It contains leaf selectors and associates to card and port profiles. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpineP The spine profile is a template used for deploying the leaf fabric configuration. It contains spine selectors and associates to card and port profiles. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:PodP A POD profile. This is a template used for deploying POD level configuration. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LePortP The leaf fabric port profile contains leaf port selectors that can associate with their respective policy groups. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpPortP A spine port profile contains leaf port selectors that can associate with their respective policy groups. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ANodeP Node Profile: It represents the template used for deploying node
fabric configuration |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:NodeP The node profile enables you to specify which nodes (Example: a leaf) to configure. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:SpineP Spine Profile Spine Access Policy: It represents the template used for deploying node
access configuration (ex. Configuration for connecting hypervisor, Fex, External
network ) |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccCardP The module profile enables you to specify the modules you want to configure. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AttEntityP The attached entity profile provides a template to deploy hypervisor policies on a large set of leaf ports. This also provides the association of a Virtual Machine Management (VMM) domain and the physical network infrastructure. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:FexP The FEX profile enables you to configure FEX interfaces. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:FuncP The hypervisor management function provides the policies used for hypervisor management and connectivity. For example, an endpoint group and encap VLAN. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:PodP Pod Profile: It represents the template used for deploying POD
level configuration |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AccPortP The interface profile enables you to specify the interface you want to configure. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:ProtPol The VPC protection policy is a container of VPC protection groups; it enables you to select a pairing type for creating the protection groups |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpCardS A card selector. This is a range of cards on the spine. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:CardS The module selector enables you to select the modules to configure and the configuration method. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:ANodeS An abstraction of the fabric node and access node selectors. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
condition:NodePolGrp The node policy group is a group of nodes to which Fault, Event, Audit, or Health record retention policies can be applied. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
firmware:FwGrp A firmware group is a set of nodes to which a firmware policy may be applied. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
maint:MaintGrp The maintenance group is a set of nodes to which a maintenance policy may be applied. The maintenance policy determines the pre-defined action to take when there is a disruptive change made to the service profile associated with the node group. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
telemetry:FlowServerGrp
Telemtry Flow Server Group. A set of nodes to which a telemetry filter policy
may be applied.
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LeafS The leaf selector. This enables you to select all or a range of leaves. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SpineS The spine selector. This enables you to select all or a range of spines. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ConnNodeS The connectivity selector is used for grouping ports between the FEX and the host (such as hypervisor). |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infrazone:NodeGrp Infrastructure Zone Node Group: Used for listing member nodes of the zone |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
mgmt:NodeGrp The managed node group captures the set of nodes that will participate in the management network. All the nodes, a range of nodes, or a specific node can be selected to participate in a given managed node group. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:LeafS The leaf selector enables you to select the interface to configure. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
condition:PodPolGrp
A set of PODs to which a set of Fault/Event/Audit/Health policies
may be applied.
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
firmware:PodFwGrp
POD Firmware Group. A set of PODS to which a firmware policy
may be applied.
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
maint:PodMaintGrp
POD Maintenance Group. A set of PODs to which a maintenance policy
may be applied.
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:PodS The POD selector enables you to select all or a range of PODs. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:APortS An abstraction of the fabric port selector and access port selector. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:LFPortS The leaf fabric port selector. This object enables you to specify leaf fabric ports with your leaf fabric port profile. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:SFPortS The spine fabric port selector. This enables you to specify spine fabric ports with your spine fabric port profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:PortS An abstraction of access interface selectors. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ConnFexS The Connectivity FEX selector is used for grouping ports between the FEX and the host (such as a hypervisor). |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:HConnPortS The host connectivity port selector is used for grouping ports between the node and the host (such as hypervisor). |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:HPortS The Host Port Selector is used for grouping ports between the node and the host (such as hypervisor). |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:SHPortS Spine Host/Access Port Selector. This selector is used for applying infrastructure
policies on selected ports |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:CtrlrS The fabric controller group is made up of a core and a tech support export policy. |
|
|
|
├
|
![[V]](styles/eye.gif) |
hvs:ExtPol The extended policies, which are common policies for VM interfaces. For example, when implementing VMware, this represents the distributed virtual port group. |
|
|
├
|
![[V]](styles/eye.gif) |
fabric:ExtPol The configuration of the extended fabric equipment, such as FEX. |
|
|
├
|
![[V]](styles/eye.gif) |
fabric:MaintPol The maintenance policy. This is used for listing blacklisted or inactive devices. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:OOServicePol The service policy. This is used for listing equipment under maintenance. |
|
|
├
|
![[V]](styles/eye.gif) |
fabric:ProtChainP A node proxy IP profile. This is an implicit profile used for managing spine proxy IP addresses. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:HIfPol The host interface policy specifies the layer 1 parameters of host facing ports. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
bgp:PeerPfxPol The peer prefix policy defines how many prefixes can be received from a neighbor and the action to take when the number of allowed prefixes is exceeded. This feature is commonly used for external BGP peers, but can also be applied to internal BGP peers. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
coop:Pol The COOP policy contains groups of Oracles nodes and COOP repositories. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:EpRetPol The endpoint retention policy provides the parameters for the lifecycle of the endpoints. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
igmp:ASnoopPol Restricts flooding of multicast traffic by sending multicast traffic only to the bridge domains that are subscribed to a particular multicast group. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
igmp:SnoopDef The process of listening to Internet Group Management Protocol (IGMP) network traffic. The feature allows a network switch to listen in on the IGMP conversation between hosts and routers. By listening to these conversations the switch maintains a map of which links need which IP multicast streams. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
igmp:SnoopPol The IGMP snooping policy streamlines multicast traffic handling for VLANs. By examining (snooping) IGMP membership report messages from interested hosts, multicast traffic is limited to the subset of VLAN interfaces on which the hosts reside. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
mld:SnoopDef The process of listening to Multicast Listener Discovery (MLD) network traffic. The feature allows a network switch to listen in on the IGMP conversation between hosts and routers. By listening to these conversations the switch maintains a map of which links need which IP multicast streams. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
mld:SnoopPol The MLD snooping policy streamlines multicast traffic handling for VLANs. By examining (snooping) MLD membership report messages from interested hosts, multicast traffic is limited to the subset of VLAN interfaces on which the hosts reside. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
bgp:CtxDef An internal object for the BGP context-level policy definition. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
bgp:CtxPol The BGP timers policy uses timers to control periodic activities such as the frequency keepalive messages that are sent to its peer, the amount of time the system waits to declare a peer dead after keepalive messages stop being received, and the amount of time before restarting a dead peer. The BGP timer policy enables you to specify the intervals for the periodic activities and supplies two options for graceful restart control: the graceful rest... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eigrp:ACtxAfPol The abstraction of the context-level EIGRP policy, which contains the configuration for an address family on a context on the node. The EIGRP policy is configured under the tenant protocol policies and can be applied to one or more contexts (private domains) under the tenant. The EIGRP context policy can be enabled on a context through a relation in the context per address family. If there is no relation to a given address family, or the EIGRP c... |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eigrp:CtxAfPol An EIGRP context policy can be applied on one or more contexts under the tenant. EIGRP context policies can be enabled on a context through a relation in the context per address family. If there is no relation to a given address family such as IPv6 or the EIGRP context policy mentioned in the relation doesn't exist, then the default context policy created under Tenant Common will be used for that address family. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
ipmc:ACtxPol Abstraction of Context-level Routed Multicast policy |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
ospf:CtxDefAf The context-level OSPF definition per address family. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
ospf:CtxPol The context-level OSPF timer policy provides the Hello timer and Dead timer intervals configuration. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
rtdmc:ACtxPol Abstraction of Context-level Routed Multicast policy |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
isis:DomPol The domain policy is used to configure IS-IS domain specific properties. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stormctrl:IfPol The storm control interface policy. A traffic storm occurs when packets flood the LAN, creating excessive traffic and degrading network performance. You can use the traffic storm control feature to prevent disruptions on ports by a broadcast, multicast, or unknown unicast traffic storm on physical interfaces. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cdp:AIfPol The CDP Interface Policy parameters. CDP is primarily used to obtain protocol addresses of neighboring devices and discover the platform of those devices. CDP can also be used to display information about the interfaces your router uses. CDP is media- and protocol-independent, and runs on all Cisco-manufactured equipment including routers, bridges, access servers, and switches. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cdp:IfPol The CDP interface policy, which is primarily used to obtain protocol addresses of neighboring devices and discover the platform of those devices. CDP can also be used to display information about the interfaces your router uses. CDP is media- and protocol-independent, and runs on all Cisco-manufactured equipment including routers, bridges, access servers, and switches. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
copp:IfPol Per interface per protocol CoPP policy |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dwdm:AOptChnlIfPol Abstract class for all the profiles for DWDM C optic channel that can be applied |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dwdm:IfPol DWDM policy that can be applied at interface level |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
lacp:LagPol The PortChannel policy enables you to bundle several physical ports together to form a single port channel. LACP enables a node to negotiate an automatic bundling of links by sending LACP packets to the peer node. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
lacp:IfPol The PortChannel interface policy defines a common configuration that will apply to one or more LACP interfaces. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
lldp:AIfPol A summary of the interface policy. We recommend you include information about where and when the policy should be used. The abstraction can be up to 128 characters. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
lldp:IfPol The LLDP interface policy, which defines a common configuration that will apply to one or more LLDP interfaces. LLDP uses the logical link control (LLC) services to transmit and receive information to and from other LLDP agents. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
netflow:ExporterPolDef Define the Netflow Exporter Policy MO which contains
internal information needed to program the leaf |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
netflow:MonitorPolDef Define the Netflow Monitor Policy MO which contains
internal information needed to program the leaf |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
netflow:RecordPolDef Define the Netflow Record Policy MO which contains
internal information needed to program the leaf |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
qos:ADppPol Define a Data Plane Policing policy. User is supposed
to use this in scenarios where the incoming traffic need
to be policed to certain levels |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
qos:DppPol Define a Data Plane Policing policy. User is supposed
to use this in scenarios where the incoming traffic need
to be policed to certain levels |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
qos:DppPolDef Define the Data Plane Policing MO which contains
internal information needed to program the leaf |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:AIfPol An abstraction of an spanning-tree protocol interface policy. This is applicable to leaf ports and n1000v distributed virtual switches. Extended chassis ports have BPDU guard filter enabled by default. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:IfPol The Spanning-Tree Protocol (STP) interface policy defines a common configuration that will apply to one or more interfaces.
STP prevents loops from being formed when the interfaces are interconnected via multiple paths. Spanning-Tree Protocol implements the 802.1D IEEE algorithm by exchanging BPDU messages with other switches to detect loops, and then removes the loop by shutting down selected bridge interfaces. This algorithm guarantees that th... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:IfPolDef The read-only copy of the spanning-tree protocol interface policy. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
arp:AIfPol This object holds arp information that is operated at a
interface level |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
bfd:AIfPol Interface-level bfd abstraction policy |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
eigrp:IfPol The EIGRP interface policy, which defines a common configuration that will apply to one or more EIGRP interfaces. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:AIfPol The neighbor discovery interface policy defines a common configuration that will apply to one or more neighbor discovery interfaces. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:IfPol The neighbor discovery interface policy defines a common configuration that will apply to one or more neighbor discovery interfaces. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:IfPolDef The read only copy of the neighbor discovery interface policy. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:APfxPol The neighbor discovery prefix policy. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:PfxPol The neighbor discovery prefix policy. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
nd:PfxPolDef The neighbor discovery prefix policy definition. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
ospf:IfPol The OSPF interface-level policy information. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pim:IfPol Interface-level PIM-SM (sparse mode) policy. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dns:Prof The DNS instance information. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dns:Profile The DNS profile defines a set of DNS providers and can be deployed to a switch for tenant contexts. To deploy a DNS profile on a switch, the appropriate label has to be defined for the context deployed on switch. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
edr:ErrDisRecoverPol The error disabled recovery policy specifies the policy for re-enabling a port that was disabled due to one or more pre-defined error conditions. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
ep:LoopProtectP The endpoint loop protection policy specifies how loops detected by frequent mac moves are handled. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2:InstPol The Layer 2 instance policy is used for configuring fabric-wide layer 2 settings. Currently, this policy contains only fabric MTU and management MTU configuration. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:ADest The abstraction of an SPAN destination. The SPAN destination is where network traffic is sent for analysis by a network analyzer. A SPAN destination can be local or remote (ERSPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of SPAN sources and destinations. The destination can be either a port or an endpoint group... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:AVDest The abstraction of a VSPAN destination. The VSPAN destination is where network traffic is sent for analysis by a network analyzer. A VSPAN destination can be local or remote (VERSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of VSPAN sources and destinations. The destination can be either a port or an endpoint... |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VDest The VSPAN destination is where network traffic is sent for analysis by a network analyzer. A VSPAN destination can be local or remote (VERSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (tenant, access, or fabric) determines the allowed types of VSPAN sources and destinations. The destination can be either a port or an endpoint group. If the destination is a port, it... |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VDestDef The VLAN-based SPAN (VSPAN) destination definition. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:Dest The SPAN destination is where network traffic is sent for analysis by a network analyzer. A SPAN destination can be local or remote (ERSPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of SPAN sources and destinations. The destination can be either a port or an endpoint group. If the destination is a port, it shoul... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:ASrcGrp The abstraction of a SPAN source group. The SPAN source group can contain a group of SPAN sources, which is where network traffic is sampled. A SPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access SPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric SPAN). When you create a traffic monitoring session, you must select a SPAN source group and a SPAN destination. The type of session (Tenan... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:SrcGrp The SPAN source group can contain a group of SPAN sources. A SPAN source is where network traffic is sampled. A SPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (access SPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric SPAN). When you create a traffic monitoring session, you must select a SPAN source group and a SPAN destination. The type of session (Tenant, Access, or Fabric) determines... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:SrcGrpDef The SPAN source group definitions. The SPAN source is where traffic is sampled. A SPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (access SPAN), a Layer 2 bridge domain, or a Layer 3 context (fabric SPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (Tenant, Access or fabric) determines the allowed types of SPAN sources an... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:AVDestGrp The abstraction of a VSPAN destination group. The VSPAN destination group can contain a group of VSPAN destinations. A VSPAN destination is where network traffic is sent for analysis by a network analyzer. A VSPAN destination can be local or remote (VERSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of VSPAN so... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VDestGrp The VSPAN destination group contains a group of VSPAN destinations. A VSPAN destination is where network traffic is sent for analysis by a network analyzer. A VSPAN destination can be local or remote (VERSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (tenant, access, or fabric) determines the allowed types of VSPAN sources and destinations. The destination can be ei... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VDestGrpDef VSPAN destination group used for configuring VSPAN source group definitions. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:AVSrcGrp The abstraction of a VSPAN source group. The VSPAN source group can contain a group of VSPAN sources. A VSPAN source is where network traffic is sampled. A VSPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access VSPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric VSPAN). When you create a traffic monitoring session, you must select a VSPAN source group and a VSPAN destination. The type ... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VSrcGrp The VSPAN source group can contain a group of VSPAN sources. A VSPAN source is where network traffic is sampled. A VSPAN source can be an endpoint group (EPG), one or more ports; or port traffic filtered by an EPG (access VSPAN), a Layer 2 bridge domain, or a Layer 3 context (fabric VSPAN). When you create a traffic monitoring session, you must select a VSPAN source group and a VSPAN destination. The type of session (tenant, access, or fabric) de... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:DestGrp The SPAN destination group contains a group of SPAN destinations. A SPAN destination is where network traffic is sent for analysis by a network analyzer. A SPAN destination can be local or remote (ERSPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of SPAN sources and destinations. The destination can be either a p... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:SpanProv The SPAN destination provider is used for configuring SPAN destination provider parameters. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VSpanProv The VSPAN destination provider is used for configuring VSPAN destination provider parameters. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:InstPol The spanning Tree Protocol (STP) instance policy, which enables you to set the bridge protocol data unit (BPDU) guard policy or filter. BDPUs are packets that run the STP protocol. The specification for STP is IEEE 802.1D. The main purpose of STP is to ensure that you do not create loops when you have redundant paths in your network. Loops are deadly to a network. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vpc:InstPol The node-level vPC domain policy, which is used to specify a vPC domain and is applied to both vPC peer devices, the vPC peer keepalive link, the vPC peer link, and all the PortChannels in the vPC domain connected to the downstream device. You can have only one vPC domain ID on each device. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
bgp:InstPol The BGP Instance level policy is used to configure MP-BGP policies inside the fabric. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:ARelayP The abstract DHCP Relay profile, which is used for configuring relay parameters per bridge domain (BD). |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:RelayP The DHCP relay profile, with one or more helper addresses in it, configures a DHCP relay agent for forwarding DHCP packets to a remote server. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
psu:InstPol The power redundancy policy is for all power supply units on the fabric nodes (leaves and spines) that are consuming the power supply policy through their respective selector profile policy. |
|
|
|
├
|
![[V]](styles/eye.gif) |
lbp:Pol The load balancing policy options for balancing traffic among the available uplink ports. Static hash load balancing is the traditional load balancing mechanism used in networks where each flow is allocated to an uplink based on a hash of its 5-tuple. This load balancing gives a distribution of flows across the available links that is roughly even. Usually, with a large number of flows, the even distribution of flows results in an even distributi... |
|
|
|
├
|
![[V]](styles/eye.gif) |
fc:AllocEncapCont Represents the container object used for managing Fibre Channel Encap Block |
|
|
├
|
![[V]](styles/eye.gif) |
fc:APinningLbl Fiber Channel Pinning Label. Its used for pinning host interfaces to uplink interfaces. This label should match with the name of a fc:PinningP configured this tenant or tenant-commmon. Once this label is configured under a fv:RsFcPathAtt, that host interface will get pinned to the uplink interfaces specified in the Pinning profile. |
|
|
├
|
![[V]](styles/eye.gif) |
fc:APinningP Abstract Fiber Channel Pinning Profile. Its used for pinning host interfaces to uplink interfaces. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fc:PinningP Fiber Channel Pinning Profile. Its used for pinning host interfaces to uplink interfaces. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fc:PinningPDef Fiber Channel Pinning Profile Definition. Its used for pinning host interfaces to uplink interfaces. |
|
|
├
|
![[V]](styles/eye.gif) |
fc:ResPolCont Container for resolved Fiber Channel policies in node |
|
|
├
|
![[V]](styles/eye.gif) |
firmware:AFwP The firmware policy specifies the desired firmware version. |
|
|
|
├
|
![[V]](styles/eye.gif) |
firmware:FwP The firmware specification policy for a node. |
|
|
├
|
![[V]](styles/eye.gif) |
firmware:RepoP The firmware repository population and maintenance information. |
|
|
├
|
![[V]](styles/eye.gif) |
fmcast:SystemGIPoPol Used for enabling usage of configured system GIPo in the fabric (includes all the PODs).
@@@ In previous releases system GIPo was hardcoded and was not usable for Multipod scenarios.
@@@ In Congo, PE/APIC changes were done for configuring new system GIPo value but NXOS changes
@@@ were slipped out of Congo. Now we are introducing this knob to start using configured system
@@@ ... |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:FabricExtConnPDef Site Connectivity Profile Definition
@@@ PE will pull FabricExtConnPDef. An Outside pushed to spine will pull it. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:AIntersiteConnP Abstract Class Container for Connectivity Information for MultiSite deployments |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:IntersiteConnP Container for Unicast Connectivity Information for MultiSite deployments |
|
|
├
|
![[V]](styles/eye.gif) |
fv:AIntersiteConnPDef Abstract Class Container Def for Connectivity Information for MultiSite deployments |
|
|
├
|
![[V]](styles/eye.gif) |
fv:APathAtt An abstraction of the path the endpoint group configuration will be deployed on. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ExtStPathAtt The path the endpoint group configuration will be deployed on. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:StPathAtt The path the endpoint group configuration is deployed on. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:VNodeAtt Represent a Path on whom the EPG configuration
will be deployed.
It represents Virtual Node Attachment. If only this type of attachement is
present under an EpP then the EpP will not get instrumented on that node.
But together with VNodeAtt if any other type of PathAtt is present then EpP
will get instrumented as usual |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:PathEpDef The node and interface, or a group of interfaces, that the endpoint group is deployed on. This is an internal object used for tracking static endpoint group deployment. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:AVip Abstraction of Virtual IP address |
|
|
├
|
![[V]](styles/eye.gif) |
fv:AccP The bridge domain (BD) access profile. When created over a BD, contracts are not enforced for the BD, and the encap will be applied to all endpoint groups on this BD. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:BDHolder The bridge domain (BD) holder contains bridge domain related information. For example, in a same shared service scenario, when a context is
deployed on a node, the PE needs to get all subnets of all the associated BDs. In this case, the private Layer 3 network context contains DNs of all associated BDs,
and with that info, the node pulls down the corresponding bridge domain holders of each of the associated BDs. The bridge domain holder contai... |
|
|
├
|
![[V]](styles/eye.gif) |
fv:ConnInstrPol Every endpoint group should have a relation set to its bridge domain. If not set by the user, then the relation is set to the default Bridge Domain and the Connectivity Instrumentation Policy determines whether or not traffic will be allowed to flow to/from that EPG. This applies to all EPGs regardless of use (VMM, baremetal, L2ext, L3ext). There is also a relation from the Bridge Domain to the VRF. If this is not set by the user, then the defaul... |
|
|
├
|
![[V]](styles/eye.gif) |
fv:EPgCont An endpoint group container is an internal object that represents endpoint groups. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AEPgCont An abstract container class for endpoint groups. This is an abstract class and cannot be instantiated |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:EPgDef An internal object that represents endpoint groups is used for deployment. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AEPgDef Abstract representation of an endpoint group definition. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:ProvDhcp Internal object that points to the provider details of a DHCP relay profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AEpP Abstract representation of an endpoint profile. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AREpP Abstract representation of the resolvable endpoint profile. This is an abstract class and cannot be instantiated. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AMgmtEpP Abstract representation of the management endpoint policy for a fabric node management endpoint group. This is an abstract class and cannot be instantiated. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:InBEpP An in-band management endpoint profile for a fabric node management endpoint group. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:InstPEpP Instance Profile Management EpP for the Fabric Node Management EPG. This EpP is created per external management entity instance profile (InstP EPg). |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:OoBEpP An out-of-band management endpoint profile for a fabric node management endpoint group. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ExtEpP Abstraction of a profile created for an endpoint connected to an external router or switch. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:BrEpP The bridge endpoint profile represents L2 outside present under a tenant. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:RtdEpP A target relation to an L3 routed outside present under a tenant. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:SvcEpP Abstract representation of a service endpoint profile, such as an endpoint profile created per node in the service graph. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:ADestSummary The abstraction of a SPAN destination information summary, which is used for configuring the SPAN destination information summary. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:AEpgSummary The abstraction of a SPAN destination endpoint group (EPG) summary, which stores EPG information for SPAN. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ACtrctEpgDef An endpoint group associated with a contract can be provider or consumer. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ToEPg The destination endpoint group. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ProtEPg An endpoint group associated with a taboo policy in a given context. This is an internal object. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:FromEPg The endpoint group that traffic originates from. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:EpCP A container to hold criterion definition objects for an endpoint group. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:PolDeliveryStatus Status of policy deployment indicates if APIC has delivered/is delivering policy to node - Policy to node cannot be delivered (node is a spine). |
|
|
├
|
![[V]](styles/eye.gif) |
fv:PolMod A bridge domain policy modifier that can override the desired state of the bridge domain. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:RemotePolHolder A container existing on each node to efficiently download policies to the node. For example: filters, bridge domain, and taboo policies. This is an internal object. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:RtdEpPInfoCont A container for target relations that point to a Layer 3 routed outside and present under a tenant. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:RtdEpPInfoHolder A container for target relations to a Layer 3 routed outside and present under a tenant. |
|
|
├
|
![[V]](styles/eye.gif) |
fv:SlaDef IPSLA Policy Definition
@@@ PE will pull IPSLA Def Mo |
|
|
├
|
![[V]](styles/eye.gif) |
fv:UnkMacUcastActMod This is the bridge domain (BD) Policy Modifier for UnkMacUcastAct. In special cases, the BD Policy Modifier can override the desired state of BD. |
|
|
├
|
![[V]](styles/eye.gif) |
geo:Site The geographical site of the fabric node. |
|
|
├
|
![[V]](styles/eye.gif) |
health:EvalP The health score evaluation policy indicates the severity of the fault in percentages. |
|
|
├
|
![[V]](styles/eye.gif) |
health:LevelsP The severity of a health score, such as healthy, fair, or poor. |
|
|
├
|
![[V]](styles/eye.gif) |
iacl:AProfile Abstract class for all the profiles for CoPP Prefilters that can be applied at the node level |
|
|
├
|
![[V]](styles/eye.gif) |
infrazone:ZoneP Infrastructure Zoning Profile: This profile can be used for carving out policy deployment zones in the fabric. With zones, user can push policies to different zones at different times to prevent or minimize fabric downtime |
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:RtdOutDefRef Reference to the Routed Out Definition associated with this RtdEpP.
Existence of this mo under RtdEpP is also used as an indicator that
the RtdEpP is version 2 (i.e. pruned) RtdEpP.
|
|
|
├
|
![[V]](styles/eye.gif) |
mock:Counter This is generated and used only by internal processes |
|
|
├
|
![[V]](styles/eye.gif) |
mock:MockRoot This is generated and used only by internal processes |
|
|
├
|
![[V]](styles/eye.gif) |
mock:Stats This is generated and used only by internal processes |
|
|
├
|
![[V]](styles/eye.gif) |
mon:Pol The base monitoring policy model. |
|
|
|
├
|
![[V]](styles/eye.gif) |
mon:CommonPol The monitoring policy model for the common semantic scope, which is used when there is no corresponding policy under the more specific infra or tenant scopes. In such cases, these policies are used throughout the fabric except for objects attached to their own specific policies. |
|
|
|
├
|
![[V]](styles/eye.gif) |
mon:EPGPol Creates a container for monitoring policies associated with the tenant. This allows you to apply tenant-specific policies related to Stats Collection, Stats Export, Callhome/SNMP/Syslog, Event Severities, Fault Severities, and Fault Lifecycles. |
|
|
|
├
|
![[V]](styles/eye.gif) |
mon:FabricPol Creates a policy which acts as a container for associated fabric monitoring policies. These can include policies related to Event/Fault severity, the Fault lifecycle, and other such monitoring policies. |
|
|
|
├
|
![[V]](styles/eye.gif) |
mon:InfraPol Creates a policy which acts as a container for associated fabric monitoring policies. These can include policies related to Event/Fault severity, the Fault lifecycle, and other such monitoring policies. |
|
|
├
|
![[V]](styles/eye.gif) |
netflow:ExporterPolHolder Mo that will be attached to retrieve the DN of the
NetflowExporterPolDef that should be downloaded on the leaf in
order to program the leaf |
|
|
├
|
![[V]](styles/eye.gif) |
netflow:MonitorPolHolder Mo that will be attached to retrieve the DN of the
NetflowMonitorPolDef that should be downloaded on the leaf in
order to program the leaf |
|
|
├
|
![[V]](styles/eye.gif) |
pki:Definition This is an abstract class and cannot be instantiated. |
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:CsyncElement The file pattern, the type of pattern (include or exclude), and the symbolic name of the pattern. |
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:Ep The PKI configuration, which includes key rings and certificate authority (CA) credentials. Components of the PKI are used to establish secure communications between two devices. |
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:FabricIssuedSSLCertificate
Object representing x509 certificates issued by the APIC for a node in the Fabric
This object is implicitly created and cannot be deleted or exported in the configuration
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:FabricNodeSSLCertificate
Object representing a Cisco issued x509 certificate for a node in the Fabric
This object is implicitly created and cannot be deleted or exported in the configuration
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:Item This is an abstract class and cannot be instantiated. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:KeyRing A keyring to create and hold an SSL certificate. The SSL certificate contains the public RSA key and signed identity information of a PKI device. The PKI device holds a pair of RSA encryption keys, one kept private and one made public, stored in an internal key ring. The keyring certificate merges into the PKI device keyring to create a trusted relationship. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:TP A trustpoint (certificate authority/CA), which issues and validates (signs) digital certificates. When participating in secure communications using the public key infrastructure (PKI), a participant can verify the identity of the other party through the CA that signed the other party's public key. |
|
|
|
├
|
![[V]](styles/eye.gif) |
pki:WebTokenData The cryptographic data used for generating and verifying web tokens. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ProfileIssues Infrastructure Profile Configuration Issues. The delegatable class is infra:Profile, which should be a super
class of all infra profiles such as Attachable Profile, Node Profile, Port Profile, Function Profile, etc. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:OosPathIssues An object used for reporting configuration issues related to port out-of-service policy. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AConfIssues The configuration issues found during the endpoint profile instrumentation in the node. This is an abstract class and cannot be instantiated. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:CompIssues The compute configuration issues for each endpoint profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:NwIssues The network configuration issues for each endpoint profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:StorageIssues Represents the storage configuration issues for each endpoint profile. |
|
|
├
|
![[V]](styles/eye.gif) |
pol:ConsElem Represents a policy consumption qualifier element. |
|
|
|
├
|
![[V]](styles/eye.gif) |
pol:If Represents an interface exposed or consumed by a policy. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pol:ProvIf Represents a function or service provider interface. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:AIf The abstraction of an interface. A contract interface and bundle interface inherits from this class. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:CPIf A contract interface is used as a contract consumption interface when
a consumer consumes the contract by associating it to a consumption interface
provided by the provider in the consumer's domain. A consumer can associate
with the contract consumption interface when it is provided by the provider in the consumer's
domain.
Note that a contract consumption interface represents one or more subjects defined under the
contract. By associating... |
|
|
|
├
|
![[V]](styles/eye.gif) |
pol:Lbl Represents a policy label. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:ALbl The identification of the DHCP provider. If the owner is the tenant, then the label is matched with the
DHCP label present under the bridge domain (BD). If the owner is the infra, then the label is matched with the DHCP label
present under the infra (and associated with the node). If n providers match the label, then all of them get configured as relay. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dhcp:Lbl A DHCP relay label contains a name for the label, the scope, and a DHCP option policy. The scope is the owner of the relay server and the DHCP option policy supplies DHCP clients with configuration parameters such as domain, nameserver, and subnet router addresses. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dns:Lbl The network domain name label. Labels enable classifying which objects can and cannot communicate with one another. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
extnw:ALIfP An abstract logical interface profile. This object defines the characteristics that will be applied to resources that match with the profile name. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:AIfP The abstraction of an interface profile. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:LIfP The logical interface profile defines a common configuration that can be applied to one or more interfaces. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:LIfPDef The interface identifiers attached to the node profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:AIfP An abstract interface profile. This encapsulates common behavior / configuration that will apply to one or more L3 external interfaces. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:LIfP The logical interface profile, which defines a common configuration that can be applied to one or more interfaces. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:LIfPDef The interface identifiers attached to the node profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:ALNodeP An abstract logical node profile. This defines the characteristics to be applied to resources that match with the profile name. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:LNodeP The logical node profile defines a common configuration that can be applied to one or more leaf nodes. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:LNodePDef The logical node profile definition. This defines the characteristics to be applied to resources that match with the profile name. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:AConsLbl Represents Abstraction of Logical Outside Profile Consumer Label. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:ConsLbl Represents Logical Outside Profile Consumer Label. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:ConsLblDef Represents Logical Outside Profile Consumer Label Definition. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:ALNodeP An abstract logical node profile. This defines the characteristics to be applied to resources that match with the profile name. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:LNodeP The logical node profile defines a common configuration that can be applied to one or more leaf nodes. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:LNodePDef The logical node profile definition. This defines the characteristics to be applied to resources that match with the profile name. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
rtctrl:LNodeP The node classification criteria for the route control context. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:Lbl The tenant or provider characteristics of the port. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:IfLblDef The tenant/provider's external connection characteristics of the port. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:NodeLblDef The tenant or provider's external connection characteristics of the port. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:AProvLbl Represents Abstraction of Logical Outside Profile Provider Label. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:ProvLbl Represents Logical Outside Profile Provider Label. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:ProvLblDef Represents Logical Outside Profile Label Definition. Defines the characteristics that
will be applied to Layer3 Outside that matches with the label name |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vsvc:AConsLbl This is generated and used only by internal processes. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
pol:ProvLbl Represents a function or service provider label. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:SpanLbl The SPAN label is used for SPAN label parameters. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ALbl The labels for filtering subjects. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ProvSubjLblDef A provider subject label definition. A subject label is used as a classification criteria for subjects being consumed/provided by the endpoint groups (EPGs) participating in the contract. The label identifies a subject being consumed by a consumer. It can be parented by 2 different methods. The first method is the relation between the consumer EPG and the contract that is used for filtering the subjects. A label should match either the subject na... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ConsSubjLbl A consumer subject label. In general, a subject label is used as a classification criteria for subjects being consumed/provided by the endpoint groups (EPGs) participating in the contract. The label identifies a subject being consumed by a consumer. It can be parented by 2 different methods. The first method is the relation between the consumer EPG and the contract that is used for filtering the subjects. A label should match either the subject n... |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ProvLbl A label used by a provider for specifying its identity. The parent can be either the provider endpoint group or the relation between the provider endpoint group and a contract. A consumer with no label will consume from all the providers of the contract regardless of the provider label. A consumer with a specific label can only consume from providers matching the label. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ProvSubjLbl A subject label is used as classification criteria for subjects being consumed/provided by the endpoint groups (EPGs) participating in the contract. The label identifies a subject being provided by a provider. It can be parented by 2 different methods. The first method is the relation between the provider EPG and the contract that is used for filtering the subjects. A label should match either the subject name or the label present under the subje... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ALblDef An abstraction of a label definition. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ConsCtrctLbl A consumer contract label. A contract label can be parented by the relation between an endpoint group (EPG) and security group. The EPG is associated with a group and lists all contracts it provides out of the group, as well as, optionally, contracts that it chooses to consume. If no consumption contracts are indicated, all contracts are consumed. If no provider contracts are identified, the EPG provides no contracts out of this group. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ConsLbl A label used by consumers to filter the providers. The label can be parented as follows:
By the consumer endpoint group.
By the relation between the consumer endpoint group and contract.
By the relation between the contract interface and contract.
By the relation between the consumer endpoint group and contract interface.
A consumer with no label will consume from all the providers of the contract with no labels. A consumer with a specific label... |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ProvCtrctLbl A label identifying a contract. A contract label can be parented by the relation between an endpoint group (EPG) and security group. The EPG is associated with a group and lists all contracts it provides out of the group, as well as, optionally, contracts that it chooses to consume. If no consumption contracts are indicated, all contracts are consumed. If no provider contracts are identified, the EPG provides no contracts out of this group. |
|
|
├
|
![[V]](styles/eye.gif) |
pol:DefRoot Represents the policy definition's subtree root. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Def An abstraction of the fabric virtualization policy definition. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AACrtrn Abstraction of Classifier used for Virtual Devices |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ACrtrn An abstraction of the classifier used for virtual devices. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Attr The attributes in the criterion. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ProtoAttr The Layer 4 protocol attributes in the criterion. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:AVmAttr The virtual attributes in the criterion. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:VmAttr The virtual attributes in the criterion. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Dom A virtual fabric domain. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ABD An abstract representation of a private layer 2 network context that belongs to a specific tenant or context, or is shared. This is an abstract class and cannot be instantiated. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ABDPol Abstract representation of a bridge domain policy. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:BD A bridge domain is a unique layer 2 forwarding domain that contains one or more subnets. Each bridge domain must be linked to a context. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:BDDef A private layer 2 network context that belongs to a specific tenant or context, or is shared. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:ACtx A private L3 network context belonging to a specific tenant. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Ctx The private layer 3 network context that belongs to a specific tenant or is shared. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:CtxDef A private L3 network context belonging to a specific tenant. This is an internal representation of the context. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Np An abstraction representing a set of requirements a group of entities has on the virtualizable fabric. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
extnw:Out An abstraction of a policy controlling connectivity to outside such as another fabric or WAN. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l2ext:Out The L2 outside policy controls connectivity to the outside. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
l3ext:Out The L3 outside policy controls connectivity to the outside. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Ap The application profile is a set of requirements that an application instance has on the virtualizable fabric. The policy regulates connectivity and visibility among endpoints within the scope of the policy. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fv:Up A set of requirements for datacenter utility functions on virtualized fabric. |
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:InfrP An abstraction of the fabric infrastructure-level policy for either fabric internal or external behaviors |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:InfrExP An abstraction of the set of rules pertaining to external fabric behavior |
|
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ExP An abstraction of an external profile. |
|
|
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:ClP The infrastructure client profile object. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fabric:InfrFP A set of rules pertaining to internal fabric behavior. |
|
|
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
mgmt:MgmtP The in-band and out-of-band management endpoint groups consists of switches (leaves/spines) and APICs.
Each node in the group is assigned an IP address that is dynamically allocated from the address pool associated with the corresponding
in-band or out-of-band management zone. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:AIpP An abstraction of a resolvable infrastructure profile. |
|
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
infra:IpP A resolvable hypervisor infrastructure profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
mgmt:ExtMgmtEntity The external entity management. The external entities (hosts) can communicate with nodes that are part of the out-of-band (OOB)
management endpoint group. To enable this communication, hosts are connected to the OOB management port of the nodes. |
|
|
|
├
|
![[V]](styles/eye.gif) |
test:Rule An abstract class for a test rule. |
|
|
├
|
![[V]](styles/eye.gif) |
pol:Ns Represents a policy namespace. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fvns:AddrInst The IP address namespace/IP address range contains unicast and multicast address blocks. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fvns:McastAddrInstP The multicast address namespace policy defines the multicast IP address ranges.
These addresses can be used for various purposes, such as VxLAN encapsulation. |
|
|
|
├
|
![[V]](styles/eye.gif) |
fvns:AInstP The namespace policy is used for managing the Encap (VXLAN, NVGRE, VLAN) ranges. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fvns:VlanInstP The VLAN range namespace policy defines for ID ranges used for VLAN encapsulation. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
fvns:VxlanInstP The VxLAN range namespace policy defines for ID ranges used for VLAN encapsulation |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:EncapInstDef The spanning-tree protocol encap instance profile definition. The segment IDs calculated using this profile are for spanning tree BPDU flooding within the fabric. It is implicitly managed by the IFC. |
|
|
├
|
![[V]](styles/eye.gif) |
pool:Pool An abstraction of a shared resource pool. |
|
|
├
|
![[V]](styles/eye.gif) |
qos:ADppPolHolder Mo that will be attached to retrieve the DN of the
qosDppPolDef that should be downloaded on the leaf in
order to program the leaf |
|
|
├
|
![[V]](styles/eye.gif) |
qos:Class The QoS classification traffic descriptor and specifications are used to categorize a packet within a specific group and making the packet accessible for QoS handling in the network. |
|
|
├
|
![[V]](styles/eye.gif) |
qos:CustomPol The custom QoS policy enables different levels of service to be assigned to network traffic, including specifications for the Differentiated Services Code Point (DSCP) value(s), and the 802.1p Dot1p priority. |
|
|
├
|
![[V]](styles/eye.gif) |
qos:CustomPolDef The definition class for a custom QOS policy. Note that this is an internal object. |
|
|
├
|
![[V]](styles/eye.gif) |
qos:DppPolDefCont Container for all the qos:DppPolDef, under top, to
have them neatly organized |
|
|
├
|
![[V]](styles/eye.gif) |
qos:InstPol A QOS instance policy, which is a container for QOS class objects. |
|
|
├
|
![[V]](styles/eye.gif) |
rtctrl:Profile The route control profile specifies policies for external networks. The layer 3 networks outside the fabric, and reachable by a Tenant's applications, route to external networks. |
|
|
├
|
![[V]](styles/eye.gif) |
snmp:APol An abstract representation of a policy. A profile contains site info and general protocol config parameters
(such as version and traps vs. informs). |
|
|
|
├
|
![[V]](styles/eye.gif) |
snmp:Inst A container for each SNMP instance. |
|
|
|
├
|
![[V]](styles/eye.gif) |
snmp:Pol The SNMP policy enables you to monitor client group, v3 user, and/or community SNMP policies.
SNMP is an application-layer protocol that provides a message format for communication between SNMP managers and agents. SNMP provides a standardized framework and a common language used for the monitoring and management of devices in a network. |
|
|
├
|
![[V]](styles/eye.gif) |
span:ASrc The abstraction of an SPAN source. The SPAN source is where traffic is sampled. A source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access SPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric SPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (Tenant, Access or fabric) determines the allowed types of SPAN sources and de... |
|
|
|
├
|
![[V]](styles/eye.gif) |
span:AVSrc The abstraction of a VSPAN source. The VSPAN source is where traffic is sampled. A VSPAN source can an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access VSPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric VSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (Tenant, Access or fabric) determines the allowed types of span sources... |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VSrc The VSPAN source, which is where traffic is sampled. A VSPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access VSPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric VSPAN). When you create a traffic monitoring session, you must select a VSPAN source and a VSPAN destination. The type of session (Tenant, Access, or Fabric) determines the allowed types of VSPAN sources and destinations. The ... |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
span:VSrcDef The VSPAN VSrcDef is used for VSPAN source definitions. |
|
|
|
├
|
![[V]](styles/eye.gif) |
span:Src The SPAN or ERSPAN source is where traffic is sampled. A source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (access SPAN), a Layer 2 bridge domain, or a Layer 3 context (fabric SPAN). When you create a traffic monitoring session, you must select a source and a destination. The type of session (tenant, access, or fabric) determines the allowed types of sources and destinations. The destination can be eithe... |
|
|
|
├
|
![[V]](styles/eye.gif) |
span:SrcDef The SPAN source definitions. The SPAN source is where traffic is sampled. A SPAN source can be an endpoint group (EPG), one or more ports, or port traffic filtered by an EPG (Access SPAN), a Layer 2 bridge domain, or a Layer 3 context (Fabric SPAN). When you create a traffic monitoring session, you must select a SPAN source and a SPAN destination. The type of session (tenant, access or fabric) determines the allowed types of SPAN sources and dest... |
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:AllocEncapBlkDef The spanning-tree protocol encap block definition for allocated IDs and the base segment ID used for the range. These segment IDs are used for spanning tree BPDU flooding within the fabric. It is implicitly managed by the IFC. |
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:UnAllocEncapBlkDef The spanning-tree protocol encap block definition for un-allocated IDs and the base Segment ID used for the range. These segment IDs are used for spanning tree BPDU flooding within the fabric. It is implicitly managed by the IFC. |
|
|
├
|
![[V]](styles/eye.gif) |
stp:AEncapCont An abstraction of a container for managing the spanning tree flooding segment ID range. |
|
|
|
├
|
![[V]](styles/eye.gif) |
stp:AllocEncapCont A container for managing the spanning tree flooding segment ID range. |
|
|
|
├
|
![[V]](styles/eye.gif) |
svccore:NodePol The core collection policy contains the system or component failure information. You can configure the policy to export a copy of the core file to a location on an external TFTP server as soon as the core file is created. |
|
|
├
|
![[V]](styles/eye.gif) |
sysmgrp:Def Abstract class for all QoS policy definitions. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:EPSelectorDef Cloud Endpoint Selector, to decide which endpointss belong
to the EPGs based on several parameters, different
selectors will be considered as OR |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:ExtEPSelectorDef Cloud Endpoint Selector, to decide which endpointss belong
to the EPGs based on several parameters, different
selectors will be considered as OR |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:EPSelector Cloud Endpoint Selector, to decide which endpointss belong
to the EPGs based on several parameters, different
selectors will be considered as OR |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:ExtEPSelector Cloud Endpoint Selector, to decide which endpointss belong
to the EPGs based on several parameters, different
selectors will be considered as OR |
|
|
|
├
|
![[V]](styles/eye.gif) |
cloud:AEPgSelector EPG Selector to correlate the cloudEPg with the corresponding fvAEPg from which it can inherit all the security policies. This is optional |
|
|
|
├
|
![[V]](styles/eye.gif) |
traceroutep:TrEp The traceroute source is the endpoint source information of the traceroute connected to ToR. |
|
|
|
├
|
![[V]](styles/eye.gif) |
traceroutep:TrExtEp Traceroute an External IP address from an End Point learned as being connected to ToR |
|
|
|
├
|
![[V]](styles/eye.gif) |
traceroutep:TrNode The traceroute for a ToR node allows you to determine the path a packet takes to get to a destination from a given source by returning the sequence of hops the packet traversed. |
|
|
├
|
![[V]](styles/eye.gif) |
trig:Inst An abstraction of a generalized system trigger. |
|
|
├
|
![[V]](styles/eye.gif) |
trig:SchedP The scheduler policy enables you to schedule a recurring or one-time window for the execution of a task. Multiple scheduler policies can be created for the same time period. |
|
|
|
├
|
![[V]](styles/eye.gif) |
trig:SingleTriggerable A triggerable object that can be triggered only once for each instance of a scheduler window. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
callhome:InvTrig When you manually trigger an inventory alert group message and do not specify a destination profile name, a message is sent to all active profiles that have either a normal or periodic subscription to the specified alert group. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
dbgexp:TechSupTrig This object is managed internally and should not be modified by the user. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
maint:MaintTrig Triggerable object on which the scheduler triggers a callback for maintenance. |
|
|
|
├
|
![[V]](styles/eye.gif) |
trig:Test An internal object for testing if an object can be triggered. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsFuncConn An abstract function node connector is used to map a service graph interface with the device interface. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsConnection An abstract connection connects two abstract connectors. These connections can either be between two abstract nodes or between an abstract node and an abstract terminal node. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:AGraph A service graph is an ordered set of function nodes between a set of terminals, which identifies a set of network service functions that are required by an application. Service functions within a graph are automatically provisioned on a service device that is based on an application's requirements. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsGraph The abstract graph is made up of abstract nodes and used to define the traffic flow through a service function such as load balancing, SSL offload, and firewall. Abstract nodes are comprised of service nodes such as a service node balancer (SLB) or firewall (FW), abstract term nodes (the nodes that are connected to endpoint groups), and connections. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:GraphInst The instance of a service graph. All instance objects are implicit. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:NodeInst An instance of a function node. A service graph consists of multiple function nodes.. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:NodeInstDef An instance of the service node. This is an internal object. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsNode An abstract node represents a service node such as a server load balancer (SLB) or firewall (FW). An abstract node is contained in an abstract graph. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsTermNode An abstract terminal node. Abstract terminal nodes are typically attached to the endpoint groups, and are connected to the abstract graph (AbsGraph) through an abstract connection (AbsConnection). |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:StsVNode A VNode. Holds the resources allocated to render a node instance on a specific Cdev. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:VNodeDef The virtual node definition. This object is used internally. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsDevCfg A shared configuration for a logical device in the L4-L7 device cluster. This configuration can be shared across multiple logical devices. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsFuncCfg The configuration for a function. This configuration can be shared across multiple functions. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsFuncProf An abstract function profile includes the abstract device configuration, the abstract group configuration, and the abstract function configuration. These are analogous to the function configuration, group configuration, and device configuration within a device. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:AbsGrpCfg The shared configuration for a function group. This configuration can be shared across multiple logical groups. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:BDDef A bridge domain definition for tracking allocated bridge domains. This is an internally used object. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:CfgDef GraphInst contains a copy of the per logical device shared configuration. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vns:DevCfgInst GraphInst contains a copy of the per logical device shared configuration. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:EPgDef An object used to track allocated endpoint groups. This object is used internally. |
|
|
├
|
![[V]](styles/eye.gif) |
vns:SvcGraphVersion The version of the entire service graph model. This is validated against the device script APIC model version. This number is of the form x.y, where x represents the major version number and y represents the minor version number of the service graph model. Guidelines: 1. The minor version is increased whenever a backward compatible change is made. This could include adding new properties or managed objects in the service graph model. It is expect... |
|
|
├
|
![[V]](styles/eye.gif) |
vz:ACollection The abstraction of a contract collection. A collection can be a single contract, a collection of all contracts associated with a bundle, or a collection of all contracts associated with a group. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ACtrct An abstraction of a resolvable contract. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:ABrCP An abstraction of a binary contract profile. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:BrCP A contract is a logical container for the subjects which relate to the filters that govern the rules for communication between endpoint groups (EPGs). Without a contract, the default forwarding policy is to not allow any communication between EPGs but all communication within an EPG is allowed. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:OOBBrCP An out-of-band binary contract profile can only be provided by an out-of-band endpoint group and can only be consumed by the external prefix set. A regular endpoint group cannot provide or consume an out-of-band contract profile. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:Taboo A Taboo contract provides a way for an endpoint group to specify the subjects on which communication is not allowed. |
|
|
├
|
![[V]](styles/eye.gif) |
vz:ACollectionDef An abstraction of a collection definition. A collection is a contract |
|
|
├
|
![[V]](styles/eye.gif) |
vz:AContDef An abstraction of a container definition. |
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:DirAssDef A direct association definition for a collection. A collection is a contract. |
|
|
├
|
![[V]](styles/eye.gif) |
vz:AFilterable An abstraction of a filter object. The filter object is a filter. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
actrl:Flt The filter rules identifying a group of filter entries. |
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:AFilter An abstraction of a filter. A filter is a group of resolvable filter entries. Each filter entry is a combination of network traffic classification properties. Note that this relation is an internal object. |
|
|
|
|
|
├
|
![[V]](styles/eye.gif) |
vz:Filter A filter policy is a group of resolvable filter entries. Each filter entry is a combination of network traffic classification properties. |
|
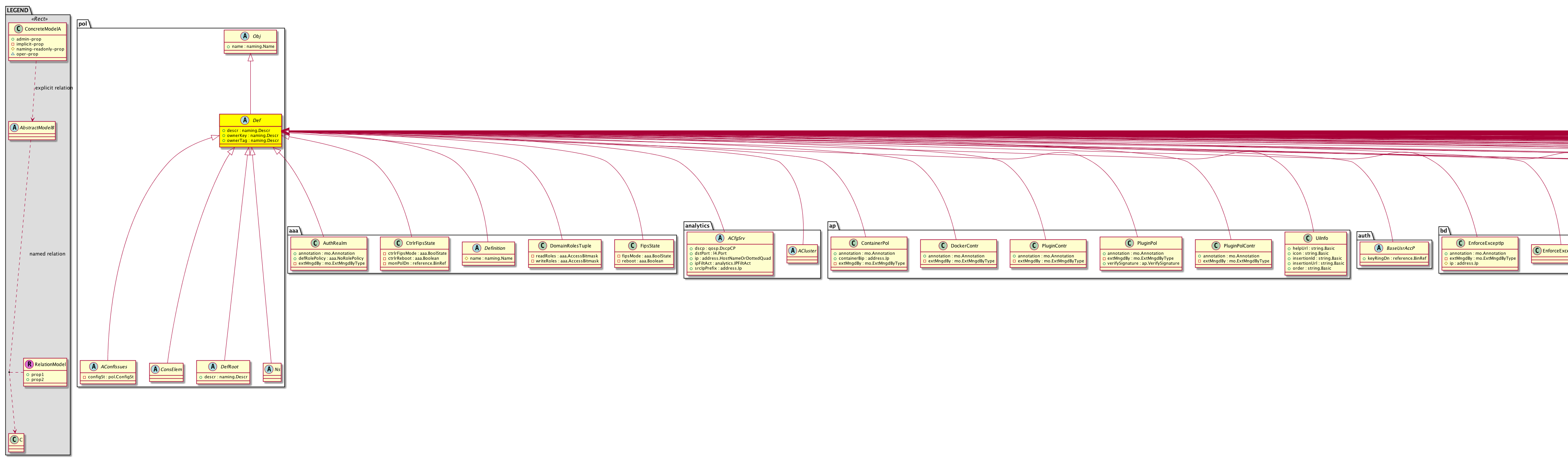
![[V]](styles/eye.gif)